Chinese cyber spies may be watching you, experts warn
Story highlights
- Despite repeated denials, China's track record points to participation in cyber espionage
- CNN's "Declassified" reveals an FBI operation to catch a Chinese spy, Sunday, 10 p.m. ET/PT
Program note: See the dramatic story of how the United States caught and convicted an American who was spying for China. Watch CNN's "Declassified," Sunday at 10 p.m. ET/PT.
(CNN)About a year ago, China and the United States formally agreed not to conduct or knowingly support the cyber theft of each other's intellectual property.
So, how is that agreement working out?
Not great, said Adm. Mike Rogers, head of US Cyber Command.
"Cyber operations from China are still targeting and exploiting US government, defense industry, academic and private computer networks,"Rogers said last April during testimony before a US Senate committee.
Cyber theft of US trade secrets can easily ruin American businesses and result in higher prices for consumers. Even more worrisome, stolen American military secrets could put US servicemen and women at risk during combat.
"Russia and China are growing more assertive and sophisticated in their cyber operations," White House spokesman Josh Earnest told reporters last July.
China's cyber tactics may be getting "more assertive," but the number of China-based hacking instances against the US government and American companies has declined in the past two years, according to US cyber security firm FireEye.
Despite all the fingers pointed in its direction, Beijing has long denied any responsibility for hacks and attacks — instead blaming internal "criminals" and rogues.
In 2004, an FBI probe nabbed an American engineer named Chi Mak who was convicted of trying to send digital information about secret US Navy technology to the Chinese government. The investigation is detailed in CNN's Original Series "Declassified."
How cyber spies operate
Sometimes cyber-spy targets might surprise you. A June New York Times report described how Chinese hackers took over a "dusty old computer" at a small welding company in Belleville, Wisconsin, to stage global assaults.
"We were totally freaked out," co-owner Lori Cate told The Times. "We had no idea we could be used as an infiltration unit for Chinese attacks."
CBS News reported on how China-based spies use malware and spear phishing to allow hackers to watch you at your desk without your knowledge. Spear phishing is harmful email disguised to look like it's from a familiar business or someone you know.
The bad guys want you to open the email, click on an attachment and boom — your computer is now working for the spies.
Countries like China are turning "to proxies (to) do their bidding in order to provide plausible deniability," said Frank J. Cilluffo the director of the Center for Cyber & Homeland Security, during testimony last February before a US House committee.
Hacker groups known by names like Deep Panda, C0d0so0 (aka Codoso)have been blamed for raiding computer systems at law firms, banks and Forbes.
One group which has been "attributed to China" has been dubbed "Mofang,"reports Wired.
"Mofang has targeted government agencies in the US, military agencies in India and Myanmar, critical infrastructure in Singapore, research and development departments of automotive companies in Germany, and the weapons industry in India," Wired reported in June.
Not only could stolen data be used to copy new American products and secret military technology, Cilluffo warned it could be used as a weapon "to blackmail and recruit Americans" — potentially to be forced to act as Chinese agents.
Sometimes the espionage is about defending against an enemy.
"Beijing also selectively uses cyber attacks against targets it believes threaten Chinese domestic stability or regime legitimacy," said James Clapper, US director of national intelligence, during congressional testimony last February.
What cyber spies want
"China's aggressive collection efforts appear to be intended to amass data and secrets (military, commercial/proprietary, etc.) that will support and further the country's economic growth, scientific and technological capacities, military power, etc. — all with an eye to securing strategic advantage," Cilluffo said.
Sometimes the spying may be about getting the inside track.
Cyber spying malware has been linked to China in arbitration over islands in the South China Sea claimed by the Philippines but occupied by China,according to a report in The Hill.
An antivirus firm called F-Secure found malware linked to China on computers in the Philippines' justice department, a law firm representing a party in the dispute and members of the Asia Pacific Economic Cooperation Summit, The Hill reported.
Sometimes it's simply about copying hardware.
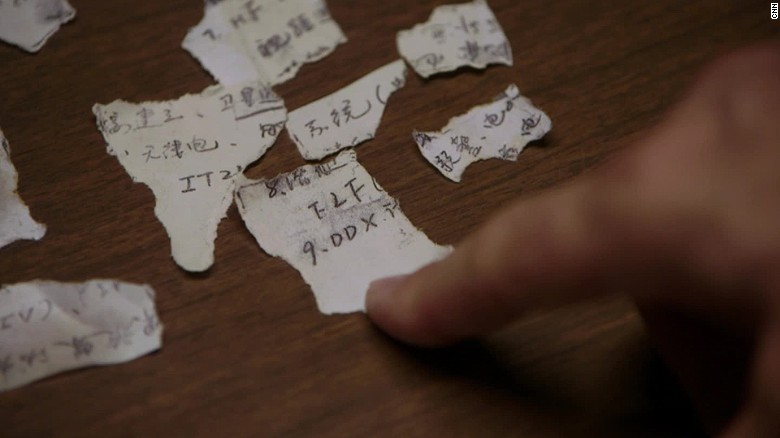
Countries can save untold money and time by stealing information that will help them duplicate rival products and weapons, instead of developing them legitimately. Last March, a 50-year-old Chinese citizen named Su Bin pleaded guilty to conspiring to hack into the computer networks of top US military contractors to pilfer sensitive information to send to China.

Last March a man admitted trying to steal data for China about Boeing's C-17 military transport.
He worked with two unidentified people for more than five years to target military data, including information about Boeing's C-17 transport plane and certain fighter jets, the Justice Department said.
Clapper: Cyber intrusions blur war and peace
Overall, China has been successful in using cyber espionage against the US government, its allies and American companies, said Clapper.
He predicts China will continue to challenge the US at "lower levels of competition," including "cyber intrusions, proxies and other indirect applications of military power — that intentionally blur the distinction between peace and wartime operations."
In other words, get used to looking over your shoulder, because it's likely that the threat of cyber espionage blamed on China will be with us for a long, long time.














No comments:
Post a Comment
Comments always welcome!